One of the ironies of employing a high-level, customer service oriented Outer Circle preventive strategy (discussed in a previous article), is that – for non-hostile individuals – it’s very difficult to understand how and why it works. The strategy does such a good job of preventing hostile attacks, and does it so subtly and unobtrusively, that it creates a situation where many of the members, employees and guests of the protected organization don’t even realize it’s there.
In many ways, this is exactly what we’re going for – prevention of hostile activity with minimal disruption to business and maximum customer service. The small tradeoff to this, however, is that to non-hostile individuals, it tends to create a false sense that nothing much is being done to protect them.
Luckily, this confusion can be dispelled by explaining how this strategy works – something I am only too happy to do.
The first step towards understanding this strategy is getting a notion of where crime in general, and hostile attacks in particular, come from. We do this by analyzing case studies and learning from the testimonies of captured attackers and hostile planners. What becomes quickly apparent is that hostile attacks don’t just come out of nowhere, and hostile attackers don’t simply materialize at their intended targets. Criminal activity is always preceded by some form of hostile planning, and usually, the bigger and more consequential the crime, the more planning that goes into it. Hostile planning is basically a decision-making process that begins by picking a specific target (out of a number of potential ones), and then nailing down the details of how, where and when to attack it. In order to achieve this, a hostile entity must first weigh the pros and cons of each potential target. One of the most consistent findings in case study research is that it’s always the easiest potential target that gets picked by the hostile entity (easiest in relative terms, compared to the other potential targets). After this, the hostile entity will spend more time observing their selected target to collect more detailed information on it.
This is where security comes into the picture.
The Circles Of Security strategy starts with an Outer Circle focus that employs:
- Deterrence By Appearance.
- Detection.
- Exposing.
Deterrence By Appearance is designed to give a potential hostile observer enough visual information to dissuade them from choosing the property in question as the final target. To do this, security doesn’t necessarily have to be aggressive or overly restrictive – solid security basics like visual projection of presence and a high level of awareness, vigilance and professionalism is usually enough.
On top of Deterrence By Appearance, the Outer Circle continues by adding an active attempt to detect and acknowledge/expose any person spending any time in the area (regardless of whether or not they seem suspicious). So even if a hostile observer wasn’t deterred by the appearance of professional security officers, being observed, acknowledged and sometimes even politely engaged by security officers, will most definitely have a strong deterring effect – additionally raising the probability that the hostile entity will either abandon its plan or take it elsewhere.
What makes this strategy so useful for facilities, campuses and special events is its ability to deter hostile planning without compromising customer service or offending non-hostile individuals (it’s one of those rare cases where you can make an omelette without breaking any eggs). This is because hostile planners observe a potential target with a very different mindset than that of a non-hostile individual. While looking for the easiest potential target, and then collecting pre-attack information on it, a hostile planner is extremely careful not to lose the element of surprise or to get exposed. Hostile planners are therefore extremely aware of, and hypersensitive to, any attention they might receive – most notably from law enforcement or security.
It’s natural for people to think of hostile attackers as callous and ruthless individuals, and this might be true enough when talking about the attack itself. But research has shown that before the attack – during hostile planning – the opposite is the case, and hostile planners are much more cautious and sensitive than most people think. An attacker might not necessarily be afraid to get harmed during the attack, but the planner (even if it’s the same person) is absolutely afraid of getting acknowledged, exposed or caught during the planning stage. A hostile planner is therefore very susceptible to any indication that a potential target might not be as good/easy as another, and this is exactly the vulnerability that this strategy targets. It’s not about scaring anyone away, it’s about painting a less favorable picture to those looking for an easy target – therefore making it more likely that they’ll either abandon their plan or take it elsewhere.
The misconceptions that many people have about this strategy (that security isn’t doing anything, that it’s “security theater”, etc.) usually have two root causes:
- A big irony in preventive security is that the more effective it is, the harder it is to measure its success (because nothing bad ever happens). It’s akin to the modern misconception about the importance of vaccines – which have been so quietly effective at preventing, and even eradicating dangerous diseases, that many people no longer understand why they’re so necessary.
- This strategy is calibrated to target the specific vulnerabilities of hostile planners. Non-hostile planners – who have nothing to hide, and are at no risk of exposure – have no reason to notice what is actually going on.
I never blame anyone for having these misconceptions because that simply means you’re a decent, non-hostile individual – the kind of person this strategy is designed to welcome, rather than deter. And the fact that non-hostile individuals have these misconceptions in the first place is actually a testament to how successfully effective yet non-intrusive this strategy is.

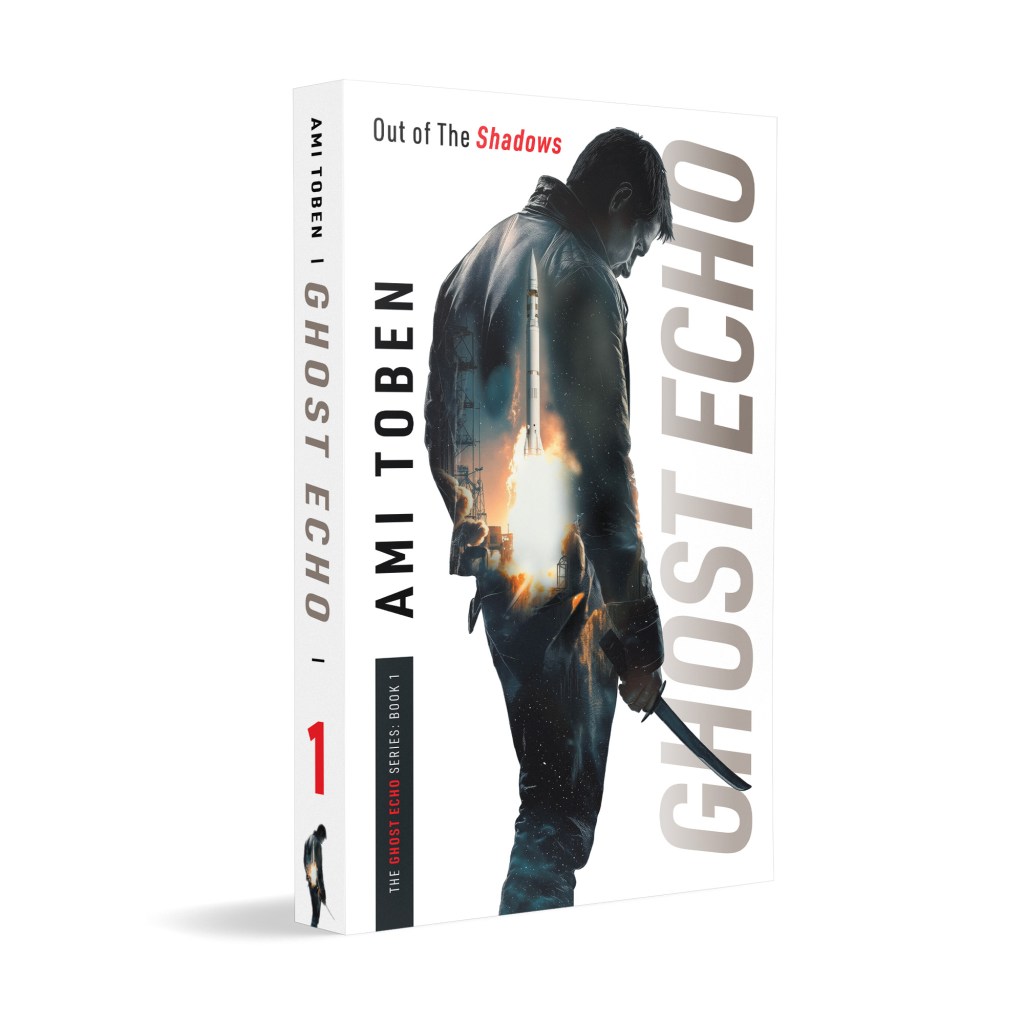
Learn more about this subject—and many others—in my master class on Hostile Activity Prevention.
Utilizing Israeli know-how and delivered by me, Ami Toben, this online course teaches actionable, time-tested methods of prevention, detection and disruption of hostile attacks.



Thank you for another useful article. Your writing is clear, and you explain concepts and procedures well. I look forward to the book.
Like the article a lot Ami. Once agin a clear and insightful look at the reality of security concepts that are effective, even if most frequently they are miss-understood.
[…] Inner Circle Since I’ve already discussed the Outer Circle at length in previous articles, let’s briefly go over the Inner Circle. The general idea of the Inner Circle is to control the […]
[…] as the ability of an operator to visually keep track of an area of interest – usually an Outer Circle to a property of interest. It’s not that you’re physically controlling the area, it’s that […]
[…] controlled scenarios or in more open-ended environments. Red Team exercises can test anything from outer-perimeter visual control to inner-circle access control. They can take the form of anything from Red-Zone […]