The private security sector is often referred to as a solution-based industry. Clients with security concerns hire security professionals who provide security solutions. But a strange issue I often find is that many people (both in and out of the industry) don’t give enough thought to what the solutions are for. In other words, what are the problems you’re trying to solve?
It’s surprising how many people miss this simple point and then go on to deploy the wrong type of solution to a problem that wasn’t fully understood. I often find this happening when it comes to solutions like surveillance detection, executive protection and covert security, which many people consider to be ‘cool’ or ‘sexy’, but don’t exactly understand which problems these solutions target, and how. And don’t get me wrong, I’m not saying these aren’t ‘cooler’ or ‘sexier’ solutions than, say, conventional campus security, just that they’re not always, or necessarily the best solutions for any problem.
The best solution providers I know are the ones who really take the time to understand the problems they’re addressing – where they come from and how they actually manifest themselves. If you want to keep an area clean, it’s worth understanding a thing or two about dirt, where it comes from and how it keeps accumulating. Otherwise you might waste time and energy running in circles, dusting and sweeping all day-every day.
Once you’ve identified and understood a security problem, the next step is to decide what part of the problem you want to solve, and how. One of the key things about solving security problems (or mitigating risks, as we often put it) is to identify what stage of the potential threat you’d like to mitigate. After all, threats don’t just pop out of thin air. They have to come from somewhere , and that somewhere always includes some form of planning on the part of the hostile entity. So the question becomes, do you want to deal with the physical threat after it arrives or do you want to target the hostile planning process that happens before the threat materializes, or both?
There are no absolute right or wrong answers here. It all depends on the situation, the specific problems and the desired outcomes. There are numerous ways of dealing with potential threats, But the point I want to emphasize here is that it can be quite silly to provide an answer if a well-defined question hasn’t even been asked. Solutions must be specifically directed at well-defined problems in order to mitigate them. Vaguely defined problems often yield ineffective and/or wasteful solutions. To overlook this basic principle and just go with a solution that looks good, or that you think is cool, is ill-advised.
Define the problem first; then find a solution that addresses it correctly.

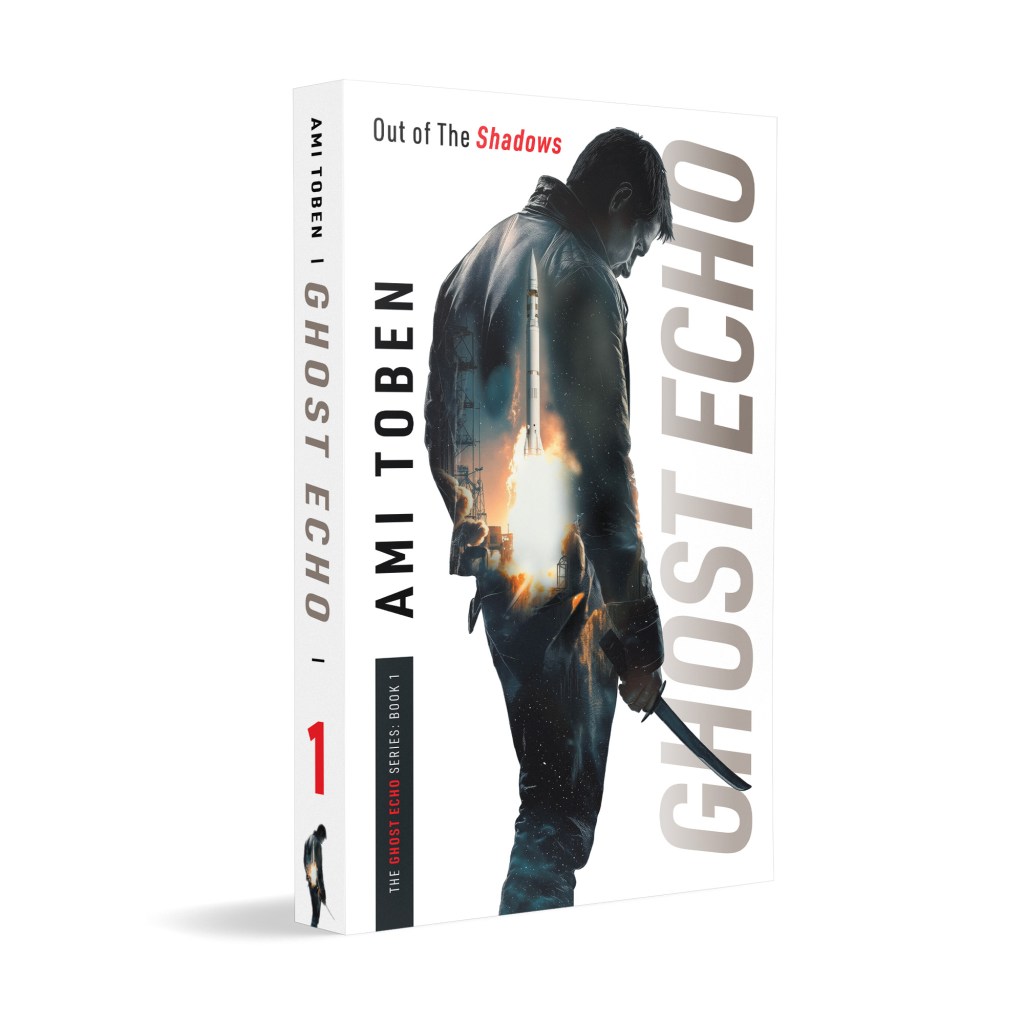
Learn more about this subject—and many others—in my master class on Hostile Activity Prevention.
Utilizing Israeli know-how and delivered by me, Ami Toben, this online course teaches actionable, time-tested methods of prevention, detection and disruption of hostile attacks.



sometimes the root causes are known but prevailing corporate cultures, unreasonable regulatory restrictions, heritage listed buildings and budgetary constraints only allow for Band-aid solutions, at best. It has been my experience that even well thought-out business plans, and cost vs. benefit analysis are not enough to change long standing firmly embedded cultures.
This issue falls right in line with my current studies on the Cooperate Problem Solving Model. This process:
Defines the Problem
Identify limiting factors
Develop potential alternatives
Analyze the alternatives
Select the best option
Implement the decision
Establish a control and evaluation system.
I have been applying this process to all my Security Risk Planning.
[…] solution, by definition, is a means of solving a problem. If a security provider can’t frame the solutions they offer in a way that answers a security […]
Excellent approach In comprehensive protection there are many very improvised “security experts” who suggest wrong security solutions.
[…] solution, by definition, is a means of solving a problem. If a security provider can’t frame the solutions they offer in a way that answers a security […]