Surveillance Detection (SD) is thankfully receiving increasing amounts of attention in recent years, as more and more industry professionals (and even some non-industry professionals) are waking up to its potential benefits.
As positive as this development is, it does create the need to abolish some misconceptions regarding SD, and to better explain how it can actually benefit real-world protective details.
In order to detect the subtle indicators of hostile surveillance, SD operators must first be well versed in surveillance operations. Generally speaking, these indicators consist of subtle correlations to the target, and possibly some subtle mistakes that might only be apparent to an SD operator who knows what to look for. It’s possible that the detection of these subtle indicators will take quite a bit of time, requiring a number of fully dedicated SD operators; which is one of the reasons why SD operations are so costly and still not all that common (though more common than before).
Now, let me make what might be a contested claim—for anyone who’s dedicated to conventional or even low profile security (including EP), even if it’s on the highest level, surveillance detection, in its purest form, is not exactly open to you. I hasten to add that this is not because of training or experience, but because of the necessity to operate covertly—without which, a potential surveillance operative would be able to know who and where the operator is, and therefore, not allow the operator to detect any subtle indicators of surveillance. It’s not a question of skill, it’s a matter of not being able to be in two places at the same time while simultaneously performing two very different roles. So, for the same reasons you can’t direct traffic at an intersection while simultaneously taking an aerial photo of the area, you can’t perform physical security (including EP) while simultaneously providing SD.
Lest you think I’m only picking on individual operators, it’s important to understand that SD is much more determined by operational parameters than it is by the individual’s skill and motivation. As qualified as a security operator might be, absent a functioning covert SD program, you’re probably not going to end up with real surveillance detection.
The good news is that even though individual qualities might be insufficient by themselves to constitute a full SD program, they can get you closer to what can be termed SD Enabled Security, which, for many organizations, turns out not only to be more realistic, but much more useful, cost effective and desirable.
The process of learning SD enabled security is not entirely different from that of pure SD. The biggest difference comes in the implementation part of it, and in the realization that if surveillance is conducted at a high enough level, we cannot realistically expect an overt, or even low profile, SD enabled security force to detect it. What we can expect, however, is to deter it.
The idea here is to combine a number of actions that will be viewed unfavorably by hostile surveillance operatives. Perhaps the most basic of these is an active projection of visual control over the area around the target, which, depending on the situation, can include an attempt to detect (and possibly acknowledge) any person spending time, or even just passing through, the area (regardless of whether or not they exhibit any surveillance indicators).
It’s important that a particularly large amount of attention be paid to the vantage points around a target. These vantage points can be plotted out by an SD professional, performing what’s called ‘Surveillance Mapping’. This special attention to the vantage points can include (but is not limited to) careful observations of people at those locations, casual acknowledgements of these people, and even polite verbal engagements.
Note that this idea of Surveillance mapping doesn’t necessarily have to entail a prolonged and comprehensive process. If a principle will be staying at a certain hotel, for example, various vantage points, both outside and inside the hotel, can be mapped out by an SD enabled advance team in a relatively short amount of time. These potential vantage points then receive special attention before, and while, the principle is in the hotel. This, of course, applies to the residence and workplace as well; where even more attention and time should be invested.
Keep in mind that a well trained surveillance operative would probably assume a vantage point only after having established a solid cover and cover story; making it unlikely that he/she will be conclusively detected by an SD enabled operator. Nevertheless, when even a skilled surveillance operative is observed, acknowledged and verbally engaged (possibly in more than one location), a strong message is being sent—namely, that security understands where to look and what to look for, and that planning, much less executing, an attack might be too risky and difficult.
It’s also important to note that there can be quite a few variations on the theme of SD enabled security, and that in addition to, or instead of, the proactive deterrence channel, a slightly more covert and reactive channel is also available. There is, as always, way more than one way to skin the hostile surveillance cat, and more than one way to combine security and surveillance detection.

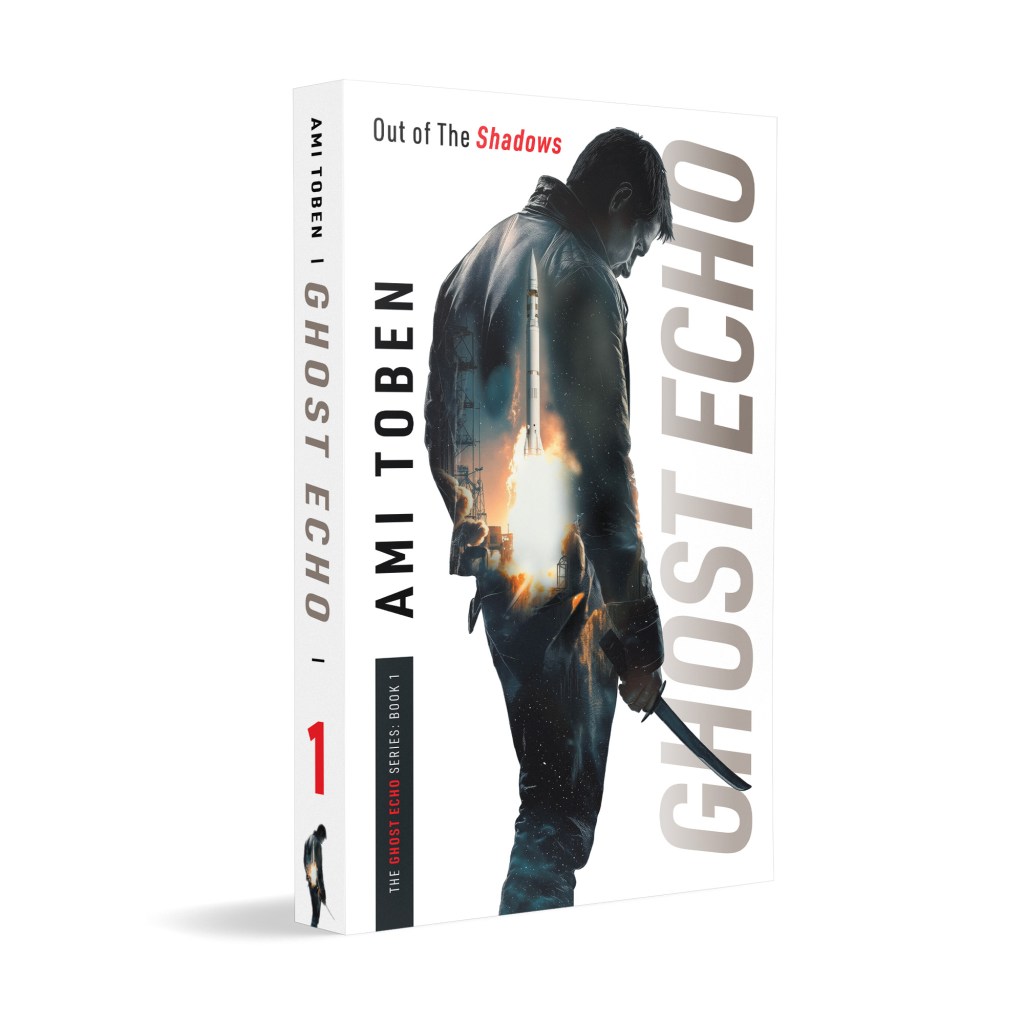
Learn more about this subject—and many others—in my master class on Hostile Activity Prevention.
Utilizing Israeli know-how and delivered by me, Ami Toben, this online course teaches actionable, time-tested methods of prevention, detection and disruption of hostile attacks.