In My last article, I explained why fundamental differences between facility security and executive protection should be reflected in surveillance detection training. In this article, I want to introduce a general strategy that can be specifically employed by facilities and campuses for detecting and mitigating hostile surveillance.
Before I jump into it, there are two important clarifications I need to make. The first is that surveillance detection and surveillance mitigation are not the same thing. The former is the detection of hostile surveillance, while the latter is the active mitigation of it. Strictly speaking, detection doesn’t have to automatically lead to mitigation, and more surprisingly, mitigation (at least in the form I’m going to present here) doesn’t necessarily depend on prior detection. These are two different activities that can either work independently or in conjunction with each other – which is what I’m recommending here.
The second point is that the general strategy I’m suggesting doesn’t come from theoretical inferences alone, but from a decade and a half of successful, field tested utilization in the San Francisco Bay Area. This strategy has its roots in Israel, but it has very importantly been calibrated and adapted to the US environment. And though in this article I’m only suggesting this strategy, let me assure you that we have been employing it very successfully in real-world field operations for over a decade and a half.
To get things started, you’ll need to separate your surveillance mitigation efforts from your surveillance detection efforts. The best way to do this is by establishing two security tiers that are staffed by two separate teams. The first tier, which consists of the bulk of your security staff, is the one that handles surveillance mitigation. These are your standard campus security officers, or possibly a select group of them. These officers don’t necessarily need to be trained on high-level surveillance detection, but rather on surveillance deterrence. The main reason for this isn’t necessarily because they’re unqualified for SD, but because these are the officers that are also responsible for the more conventional campus security operations, including: access control, internal and external patrols, ushering, directing traffic, etc. Proper surveillance detection requires that SD operators work covertly, and since campus security officers are not covert operators, there’s not much point in spending valuable resources on training them to conduct operations they’ll never be in a position to execute.
Surveillance deterrence starts by painting an unwelcoming picture for hostile surveillance to see, along with a visual projection of an active attempt to expose surveillance. Security officers should try to make it clear to the hostile entity that the target that’s being surveilled is not an easy/desirable one; making it more probable that the hostile entity will either abandon its plan or take it elsewhere.
In order to carry this out, you’ll need to start with solid security basics: good visual projection of security presence, breaking of routines (whenever possible), and generally maintaining a high level of awareness, vigilance and professionalism. This can be bolstered up by adding a somewhat less conventional set of actions that are designed to confuse potential surveillers; thereby making it more difficult for the hostile surveillance entity to understand the target and put together an effective plan of attack. Activities such as randomly photographing certain locations and people in the surrounding area, sporadically writing down license plate numbers of vehicles in the area, etc. The random nature of these actions is precisely the point. Hostile surveillance operatives are not likely to assume that such activities are randomly performed for no good reason, which might make them try to understand them better. Trying to understand such random activities will, at the very least, lengthen the process of surveillance; causing the hostile entity to increase its costs and assume more risk. This shifting of the cost/risk-benefit ratio should further raise the probability that the hostile entity will either abandon its plan or favor a different target that can be more easily understood.
At the heart of surveillance deterrence is an active projection of visual control over the area around the facility or campus, along with an attempt to detect and acknowledge any person spending any time in the area, or even just passing through (regardless of whether or not they seem suspicious). It’s important that a particularly large amount of attention be paid to the vantage points in the area. These vantage points can be located, assessed and plotted out by a surveillance detection professional, performing a service called Surveillance Mapping. After Surveillance Mapping is complete, conventional campus security officers can be instructed to pay close attention to these locations. These instructions (or post orders) should include random visits to the vantage points, performed as often as possible, along with casual acknowledgements and even polite verbal engagements of people who occupy them (regardless of whether or not they appear suspicious).
Keep in mind that a well trained surveillance operative would probably assume a vantage point only after having established a solid cover and cover story, making it unlikely that he/she will be detected or exposed as a surveillance operative by a conventional security officer. Nevertheless, when even a skilled surveillance operative is observed, acknowledged and verbally engaged in this way, a very real and very strong level of deterrence is established – additionally raising the probability that the hostile entity will either abandon its plan or favor a different target where its operatives will not be detected, much less acknowledged and engaged by security.
As for the surveillance detection element (or rather, elements of SD), this is carried out by the second tier operators. These operators, in addition to performing static SD elements, can also conduct ‘Red Team’ exercises that evaluate the surveillance mitigation team’s performance, and help maintain a continuous level of training and awareness. Though it might sound like these functions can only be performed by some unique new tier of operators, most campuses and facilities already have an existing position that, after receiving some specialized training, can provide these functions – the roaming security supervisors.
Properly trained, supported and equipped, supervisors who are usually tasked with the conventional function of security check-ups, can begin by observing the surveillance vantage points (and the rest of the ‘Red Zone’) from the outside in, in order to detect hostile surveillance. This adds an external layer and angle of detection to the already quite comprehensive internal angles that are maintained by the surveillance mitigation team. The result this produces is a ‘Red Zone’ (the zone that contains the vantage points on the target) that is observed, checked and scrutinized from at least two different angles by two types of operators in two different ways; creating an environment that is very uncomfortable and unconducive for hostile surveillance. From a traditional SD perspective, some might find each individual angle to be less than perfectly ideal on its own, but the resulting pincer maneuver, one-two combo that the ‘Red Zone’ receives from both tiers can have a formidable effect.
Is this the only way to detect and mitigate hostile surveillance on facilities and campuses? Of course not. Is this a foolproof strategy for detecting and/or mitigating hostile surveillance? of course not (there’s no such thing). Can’t you deploy a fully specialized SD team that will be completely dedicated to surveillance detection on facilities and campuses? Yes, of course you can. But over a decade of field experience, security directorship and account management have shown me that in the real world, except for a very small minority of cases, most facilities and campuses will not have the resources, budgets or indeed the willingness to employ a fully dedicated SD detail.
A big benefit of largely basing this strategy on existing budgets and human resources is that, from a business management perspective, it’s scalable, and can be applied to dozens or even hundreds of properties. As such, you’ll need to take into account the unsurprising fact that not every single facility or campus security officer will necessarily be interested in surveillance detection and mitigation. This fact is perfectly natural and perfectly fine, since the overall strategy doesn’t necessitate that every single officer be an SD operator. I’d love to be able to say that facility and campus security teams must only consist of fully committed, top-notch operators, but my experience tells me that this is somewhat unrealistic. The point here is to make the best of the material and budget you have. Officers who are interested and engaged will have an opportunity to receive more training and advance up the ranks, while those who aren’t can still contribute their part to the strategy by simply following their post orders (which include surveillance mitigation activities).
We can discuss the disadvantages of this strategy, which should not be ignored, but from my experience, the advantages far outweigh the disadvantages. For one thing, it adds more options to the all-or-nothing SD challenge. Secondly, it allows each campus and facility to tailor its own strategy to its own unique environment and circumstances, rather than accept SD conventions from other fields and environments. It allows facilities and campuses to work within their budgets, and better utilize their existing resources. And lastly (though I’m not sure why I’m putting this last), it works. Plain and simple. And I say this from experience.

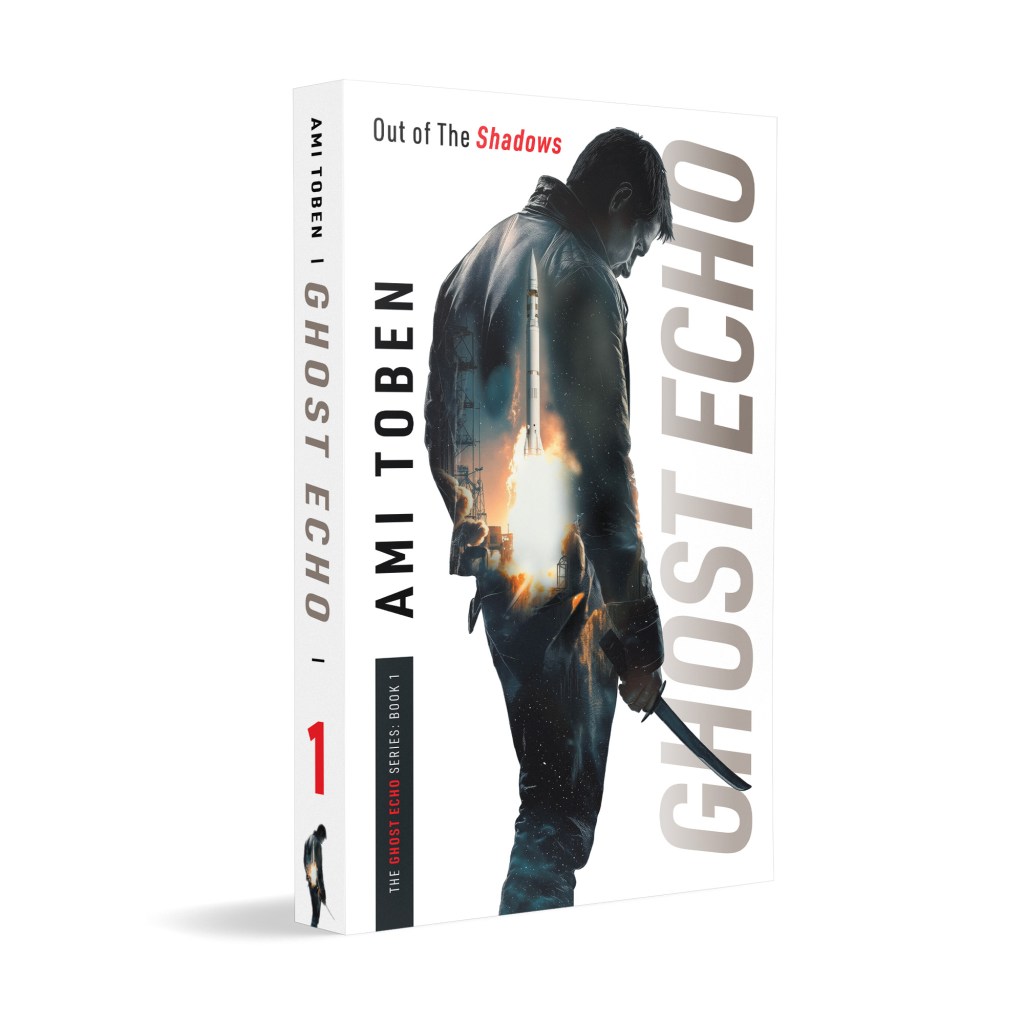
Learn more about this subject—and many others—in my master class on Hostile Activity Prevention.
Utilizing Israeli know-how and delivered by me, Ami Toben, this online course teaches actionable, time-tested methods of prevention, detection and disruption of hostile attacks.



Dear Ami
Thank you for another useful and well written article. In light of the current situation in Europe, it is timely.
Yours
Ellis
[…] makes this strategy so useful for facilities, campuses and special events is its ability to deter hostile planning without compromising customer service […]
[…] you won’t be able to stop. Detect, expose and if possible, engage anyone out there – suspicious or not. Even if this won’t necessarily lead to an advanced surveillance operative being captured, you […]